|
February 2015
In this issue
|
> |
What is the Cloud and How Can it Benefit You? |
|
> |
How to Detect Malware Symptoms |
|
> |
Revealed: Hidden Costs |
|
> |
How to Remove Duplicates in Excel 2013 |
|
> |
A Preview of Windows 10 |
|
> |
Five Actions of a Risk Aware Organization |
|
> |
Business Continuity Tip |
|
> |
Cartoon/Quote |
|
|
Five Actions of a
Risk Aware
Organization
used with permission
from IBM ForwardView

The business opportunities in cloud and mobile are increasing
our connectivity�boosting the number of devices on our network
and increasing access to data. Yet, on any given day, the
front page headlines scream about the
latest data security breach;
thieves stealing valuable business assets, including confidential
intellectual property as well as personal information about
customers and employees.
Read more
|
|
|
Business Continuity Tip
Don't Get Caught in the Cold
As
millions break out their heavy coats and bundle up for the cold temperatures,
one thing is clear - winter is officially here.
And with
the arrival of bone chilling temperatures, so comes the increased risk to your
organization and your home including:
Read more |
Please forward this newsletter to anyone else in your
organization who might be interested!
 |
What is the Cloud and How
Can it Benefit You?
 As a kid, I used to make a tin can telephone by tying a string
to each of two soup cans. When two tin cans are connected, you
can send and receive sound waves. Imagine, for a moment, that
this tin can string spans the width of your office. Two of your
employees need to communicate through the tin cans, so they
build the connection. A third employee is invited to "join the
call", so he ties his tin can to the string of the first two
cans. Then a fourth employee ties his string, then a fifth,
and so on. This concept is the very foundation on which the
Internet works: sending and receiving information over a wire
(in the tin can example, sound waves). As a kid, I used to make a tin can telephone by tying a string
to each of two soup cans. When two tin cans are connected, you
can send and receive sound waves. Imagine, for a moment, that
this tin can string spans the width of your office. Two of your
employees need to communicate through the tin cans, so they
build the connection. A third employee is invited to "join the
call", so he ties his tin can to the string of the first two
cans. Then a fourth employee ties his string, then a fifth,
and so on. This concept is the very foundation on which the
Internet works: sending and receiving information over a wire
(in the tin can example, sound waves).
The Internet is essentially one giant connection through
copper, fiber optics, and telephone lines, separated by networking
devices. These networking devices may be routers, modems, or
switches, among others. The difference between the Internet
and the tin can example is that there is not one main wire that
everyone connects to - instead, using the metaphor, the first
employee may have a direct connection to the fourth, and the
second employee may have a direct connection to the third. Imagine
two companies connecting together, and you
can see where things get tricky. The connections become entangled
and form a web, thus bringing light to the term "World Wide
Web".
Read
more |
|
How to Detect
Malware Symptoms
used with permission
from Microsoft Safety & Security Center
If your computer starts to behave strangely, you might be
experiencing spyware symptoms or have other unwanted software
installed on your computer. Here are a few tips on how to detect
malicious software:
- I see pop-up advertisements all the time. Some
unwanted software will bombard you with pop-up ads that
aren't related to a particular website you're visiting.
These ads are often for adult or other websites you may
find objectionable. If you see pop-up ads as soon as you
turn on your computer or when you're not even browsing the
web, you might have spyware or other unwanted software on
your computer.
- My settings have changed and I can't change
them back to the way they were. Some unwanted
software can change your home page or search page settings.
Even if you adjust these settings, you might find that they
revert back every time you restart your computer.
Read more |
|
Revealed: Hidden Costs
used with permission
from HP Technology at Work
 In today's era of notebooks, tablets, and smartphones, mobility
is a high priority�making small businesses more dynamic and
responsive in an on-the-go world. In today's era of notebooks, tablets, and smartphones, mobility
is a high priority�making small businesses more dynamic and
responsive in an on-the-go world.
That reality, however, should not detract from the important
role desktop PCs still play in today's business environment,
delivering more power, more robust upgrade options, and more
functionality compared to their portable counterparts.
While large enterprises typically refresh their desktop PCs
once every three years, small businesses tend to hold on to
their PCs for five to seven years [1]. Older hardware, however,
often slows operations and sparks hidden costs. In fact, PCs
more than four-and-a-half years old are estimated to cost 50
percent more to support and take 50 percent longer to perform
many tasks [2].
Read
more |
|
How to Remove
Duplicates in
Excel 2013
Very commonly you may be dealing
with a spreadsheet of data, with many duplicates that you want
to remove quickly. This happens often if you are dealing with
mailing lists with repeated information (names, email addresses,
zipcodes, etc.), an export of data from a system, or a report.
Instead of manually deleting duplicated data to trim down
your spreadsheet, use the Remove Duplicates
feature!
To demonstrate this feature, we have a simple two column
spreadsheet.
Read
more |
|
A Preview of Windows 10
 Windows 10 is the next generation of Microsoft's device OS
that adapts to the devices you're on and what you're trying
to get done, with a consistent, familiar, and compatible experience
that enables you to be more productive. Windows 10 is the next generation of Microsoft's device OS
that adapts to the devices you're on and what you're trying
to get done, with a consistent, familiar, and compatible experience
that enables you to be more productive.
Future Features
Here is a quick introduction to the first highlighted key
features of Windows 10 that are included in the released Technical
Preview. This is a sneak peak, and not an exhaustive list of
final product features. But what might we be looking forward
to?
Read
more |
|
 |
"Don't cry because it's over,
smile
because it happened."
-
Dr. Seuss
|
|
|
 |
Databranch, Inc.
132 North Union Street, Suite 108
|
Olean, New York 14760
(716) 373-4467 - Olean |
(607) 733-8550 - Corning/Elmira
www.databranch.com |
|
|
|



 As a kid, I used to make a tin can telephone by tying a string
to each of two soup cans. When two tin cans are connected, you
can send and receive sound waves. Imagine, for a moment, that
this tin can string spans the width of your office. Two of your
employees need to communicate through the tin cans, so they
build the connection. A third employee is invited to "join the
call", so he ties his tin can to the string of the first two
cans. Then a fourth employee ties his string, then a fifth,
and so on. This concept is the very foundation on which the
Internet works: sending and receiving information over a wire
(in the tin can example, sound waves).
As a kid, I used to make a tin can telephone by tying a string
to each of two soup cans. When two tin cans are connected, you
can send and receive sound waves. Imagine, for a moment, that
this tin can string spans the width of your office. Two of your
employees need to communicate through the tin cans, so they
build the connection. A third employee is invited to "join the
call", so he ties his tin can to the string of the first two
cans. Then a fourth employee ties his string, then a fifth,
and so on. This concept is the very foundation on which the
Internet works: sending and receiving information over a wire
(in the tin can example, sound waves).
 In today's era of notebooks, tablets, and smartphones, mobility
is a high priority�making small businesses more dynamic and
responsive in an on-the-go world.
In today's era of notebooks, tablets, and smartphones, mobility
is a high priority�making small businesses more dynamic and
responsive in an on-the-go world.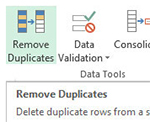
 Windows 10 is the next generation of Microsoft's device OS
that adapts to the devices you're on and what you're trying
to get done, with a consistent, familiar, and compatible experience
that enables you to be more productive.
Windows 10 is the next generation of Microsoft's device OS
that adapts to the devices you're on and what you're trying
to get done, with a consistent, familiar, and compatible experience
that enables you to be more productive.