|
June
2012
In this issue
|
> |
Mobile Security |
|
> |
Business Continuity Plan |
|
> |
Stop Mobile Malware |
|
> |
Scams and Hacks |
|
> |
How to Use Field Codes |
|
> |
Business Continuity Tip |
|
> |
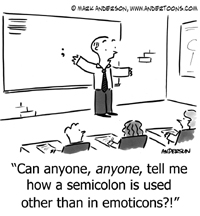
Cartoon/Quote |
|
How to Use Field Codes in Microsoft Word 2010
Field codes are
one of Microsoft Word€s key elements, frequently used by
many users. If you have ever inserted a date or a page
number to a document, you have used a field code. Despite
their heavy use, many people are unaware of how they
actually work.
What is a Field Code?
A field code is €smart€ text € when used, they can update
when needed. There are hundreds of various codes for various
purposes, one of the most common being the code for the
current date € 29at24-Ti1824 Pictu+-24. Any time the field
updates, the information within the field updates.
What Do They Do?
Field codes enable you to:
Read more
Business Continuity
Tip
Know Your Route
Whether it's a building
evacuation due to a fire or a city evacuation due to hurricane, know your
routes. And most importantly, make sure your employees know your routes.
In the event of an emergency, stairwells, exits and/or roads may be blocked.
It is important to have a plan and a backup plan in place so your employees
know when to evacuate, where to go, and what to take with them.
Please forward this newsletter to anyone else in your
organization who might be interested!

|
Mobile Security: Why
You Need to Go Beyond the Basics
used with the permission from Symantec
 Just
how quickly are enterprises adopting mobile applications? Just
how quickly are enterprises adopting mobile applications?
Very, very quickly.
According to one recent survey, as many as 71% of organizations are
using, or planning to use custom mobile applications.
"We have reached a tipping point in the business use of mobile
devices," concludes Symantec's
2012 State of Mobility Survey. "Most organizations are making
line-of-business applications available [to mobile devices]."
The reasons for this, of course, are clear: Businesses want to
improve agility, increase workplace effectiveness, and take less
time to accomplish business-critical tasks.
Read more
|
|
A Business Continuity
Plan
Gives You One Less Thing to Worry About
used with
permission from HP Technology at Work
 When
a business€s data is compromised, it€s just a matter of time
before things begin to fall apart. As a result, the
importance of having a business continuity plan in place is
never clearer than during times like these. Sometimes known
as a disaster recovery plan, a business continuity plan not
only prepares your business for how to protect its data, but
also how to prepare itself in the event of a catastrophic
power failure or natural disaster. When
a business€s data is compromised, it€s just a matter of time
before things begin to fall apart. As a result, the
importance of having a business continuity plan in place is
never clearer than during times like these. Sometimes known
as a disaster recovery plan, a business continuity plan not
only prepares your business for how to protect its data, but
also how to prepare itself in the event of a catastrophic
power failure or natural disaster.
As far as protecting your business is concerned, a business
continuity plan is also the least expensive option for small
companies because it costs virtually nothing to produce.
Utilizing tools such as HP Business Continuity and Recovery
Services, and putting the plan into practice, will
dramatically improve your chances of continuing operations
during a significant event.
Read more
|
|
How to Stop Mobile
Malware
Before the Damage is Done
used with
permission from HP Technology at Work
 The
proliferation of mobile devices has given cybercriminals a
vast and growing new ecosystem to work with. And they€re
starting to take advantage of that opportunity. According to
McAfee€s Threats Report: Fourth Quarter 2011, the number of
mobile malware samples jumped from less than 150 in the
third quarter of 2011 to well over 400 in the fourth
quarter. The
proliferation of mobile devices has given cybercriminals a
vast and growing new ecosystem to work with. And they€re
starting to take advantage of that opportunity. According to
McAfee€s Threats Report: Fourth Quarter 2011, the number of
mobile malware samples jumped from less than 150 in the
third quarter of 2011 to well over 400 in the fourth
quarter.
€Cybercriminals are going for [mobile] because people put a
lot of identifying information on their devices,€ says Karim
Hijazi, Founder and CEO of Unveillance, an IT security
intelligence provider. €But that€s a scary mistake because
devices are actually more vulnerable."
Read more
|
|
Scams and Hacks: Is
Your
Business a Target for the New Con Artist?
used with
permission from HP Technology at Work
 You
work hard for your business. You€ve logged endless hours.
You€ve put blood, sweat and tears into making your business
successful. Today, it€s easier than ever for social
engineers and hackers to take everything you€ve put into
your business (and then some) in the blink of an eye. You
work hard for your business. You€ve logged endless hours.
You€ve put blood, sweat and tears into making your business
successful. Today, it€s easier than ever for social
engineers and hackers to take everything you€ve put into
your business (and then some) in the blink of an eye.
What are social engineers? Social engineers are con
artists who take advantage of human behavior to pull off a
scam. They manipulate businesspeople into trusting and
helping them get the information they desire, using whatever
tactics necessary.
Read more
|
|
|
|
"My father didn't tell me how to live; he
lived, and let me watch him do it."
-
Clarence Budington Kelland
|
|
|
 |
Databranch, Inc.
132 North Union Street, Suite 108
|
Olean, New York 14760
(716) 373-4467 - Olean |
(607) 733-8550 - Corning/Elmira
www.databranch.com
|
|
|
|


 Just
how quickly are enterprises adopting mobile applications?
Just
how quickly are enterprises adopting mobile applications?

 You
work hard for your business. You€ve logged endless hours.
You€ve put blood, sweat and tears into making your business
successful. Today, it€s easier than ever for social
engineers and hackers to take everything you€ve put into
your business (and then some) in the blink of an eye.
You
work hard for your business. You€ve logged endless hours.
You€ve put blood, sweat and tears into making your business
successful. Today, it€s easier than ever for social
engineers and hackers to take everything you€ve put into
your business (and then some) in the blink of an eye.