
used with permission from ezMicro
 There
is a new and very serious virus named CryptoLocker that is currently
circulating the Internet. The threat involves an e-mail attachment that,
if opened, will evade most anti-virus and anti-spyware software and
encrypt data on your individual computer and your network, making it
appear to be inaccessible. Please inform everyone to be extra vigilant
about not opening attachments from questionable sources. The delivery is
very clever and very malicious.
There
is a new and very serious virus named CryptoLocker that is currently
circulating the Internet. The threat involves an e-mail attachment that,
if opened, will evade most anti-virus and anti-spyware software and
encrypt data on your individual computer and your network, making it
appear to be inaccessible. Please inform everyone to be extra vigilant
about not opening attachments from questionable sources. The delivery is
very clever and very malicious.
CryptoLocker currently has three infection vectors
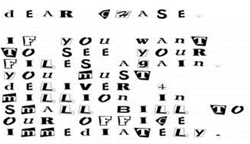
- This infection was originally spread via sent to company email addresses that pretend to be customer support related issues from FedEx, UPS, DHS, etc. These emails would contain an attachment that when opened would infect the computer
- Via exploit kits located on hacked web sites that exploit vulnerabilities on your computer to install the infection
- Through Trojans that pretend to be programs required to view online videos
You should NOT open any attachment you are not 100% confident is safe. These messages should be deleted immediately, if received.
What happens if you become infected with CryptLocker:
Once the infection is active on your computer it will scan your drives (local & network) and encrypt the following types of files with a mix of RSA & AES encryption, *.odt, *.ods, *.odp, *.odm, *.odc, *.odb, *.doc, *.docx, *.docm, *.wps, *.xls, *.xlsx, *.xlsm, *.xlsb, *.xlk, *.ppt, *.pptx, *.pptm, *.mdb, *.accdb, *.pst, *.dwg, *.dxf, *.dxg, *.wpd, *.rtf, *.wb2, *.mdf, *.dbf, *.psd, *.pdd, *.eps, *.ai, *.indd, *.cdr, *.jpg, *.jpe, *.img,*.jpg, *.dng, *.3fr, *.arw, *.srf, *.sr2, *.bay, *.crw, *.cr2, *.dcr, *.kdc, *.erf, *.mef, *.mrw, *.nef, *.nrw, *.orf, *.raf, *.raw, *.rwl, *.rw2, *.r3d, *.ptx, *.pef, *.srw, *.x3f, *.der, *.cer, *.crt, *.pem, *.pfx, *.p12, *.p7b, *.p7c.
Once all of your data is encrypted (both on your machine and any server or other machine you have access to) you will be shown a screen titled CryptoLocker that contains a ransom note on how to decrypt your files. Depending on the version of CryptoLocker that is installed, the ransom may be for $100 or $300 USD. This payment can be made via Bitcoin, MoneyPak, Ukash, or cashU. You will also be shown a countdown that states that you need to pay the ransom with 72 hours. Failure to do so will cause the decryption tool to be deleted from your computer, making your data completely inaccessible. The key to avoiding having to pay this extortion is having a good backup in place. If two machines are infected, then you will be double encrypted and the chances of unencrypting the data is near zero.
Unfortunately at this time there is no other way to retrieve the key used to encrypt your files. Brute forcing the encryption key is realistically not possibly due to the length of time required to break the key. Any decryption tools that have been released by various companies will not work with this infection. The only method you have of restoring your files is from a backup, or if you have System Restore, through the Shadow Volume copies that are created every time a system restore is performed.
The SPAM filters and other network defenses are updating continually to try to keep this threat at bay, but the users are the last line of defense. When in doubt, be safe and delete the message and call the sender if you think it may have been something legitimate that requires your attention.
Again, the key to recovering from this malware (if the network were to become infected) is having a good backup of all data. Please don€t hesitate to let us know how we can assist in making sure that all data is backed up on all of your workstations and servers.