Upcoming Changes to Microsoft Office 365 Authenticator App
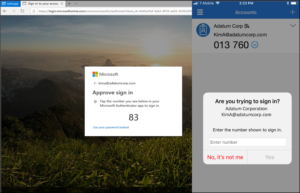
Microsoft has announced an upcoming change to the default method used in its Authenticator App. Starting May 8th, 2023, users will be required to input a verification number into the authenticator app. This date was previously February 27th, but Microsoft recently released a revision to the start date.
This number matching method is replacing the approve/deny push notification sent to mobile devices. Number matching is a key security upgrade to traditional second factor notifications in Microsoft Authenticator.
Microsoft will remove the admin controls and enforce the number match experience tenant-wide for all users starting May 8th, 2023.
Please note that this change will occur for both PCs and mobile devices. No action is required by the end users, this change will happen automatically by Microsoft.
If you have any questions regarding this upcoming change, or need any assistance, please contact Databranch Service at 716-373-4467 x4.
Microsoft Office 365 Changes to Security Defaults
Security Defaults are the preconfigured security settings that exist on your Microsoft accounts. Microsoft has announced that throughout the spring and summer of 2023, they will be rolling out Azure AD Security Defaults to all existing tenants.
Some of the changes enforced by the Security Defaults are below:
Things to watch for:
Customers will have the ability to disable the settings or configure alternate conditional access policies. However, disabling the Security Defaults would create vulnerabilities across your Microsoft accounts leaving your organization’s cybersecurity at risk.
Microsoft released Security Defaults back in 2019 to ensure that basic cybersecurity measures, such as MFA, were being used on their accounts. Because of this, over 30 million organizations already have baseline Security Defaults in place. This has allowed these companies to experience 80% less compromised accounts compared to companies without Security Defaults.
MFA alone is known for being the most effective tool at preventing compromised accounts, yet it is one of the most underutilized security measures. Microsoft’s Security Report states that MFA can block over 99.9% of account compromised attacks.
Databranch has taken the step of proactively enabling these Security Defaults for our own Microsoft tenant. This not only improves the cybersecurity of our Microsoft accounts, but it will also allow us to experience these changes first hand so we can better serve our clients.
We are also performing a review of the Office 365 tenants for all of our managed clients, so that we can proactively get their Security Defaults enabled, if they are not already.
Reach out today at [email protected] or 716-373-4467 if you have questions about these changes or wish to speak with one of our team members about enabling MFA for more accounts.
comments powered by Disqus